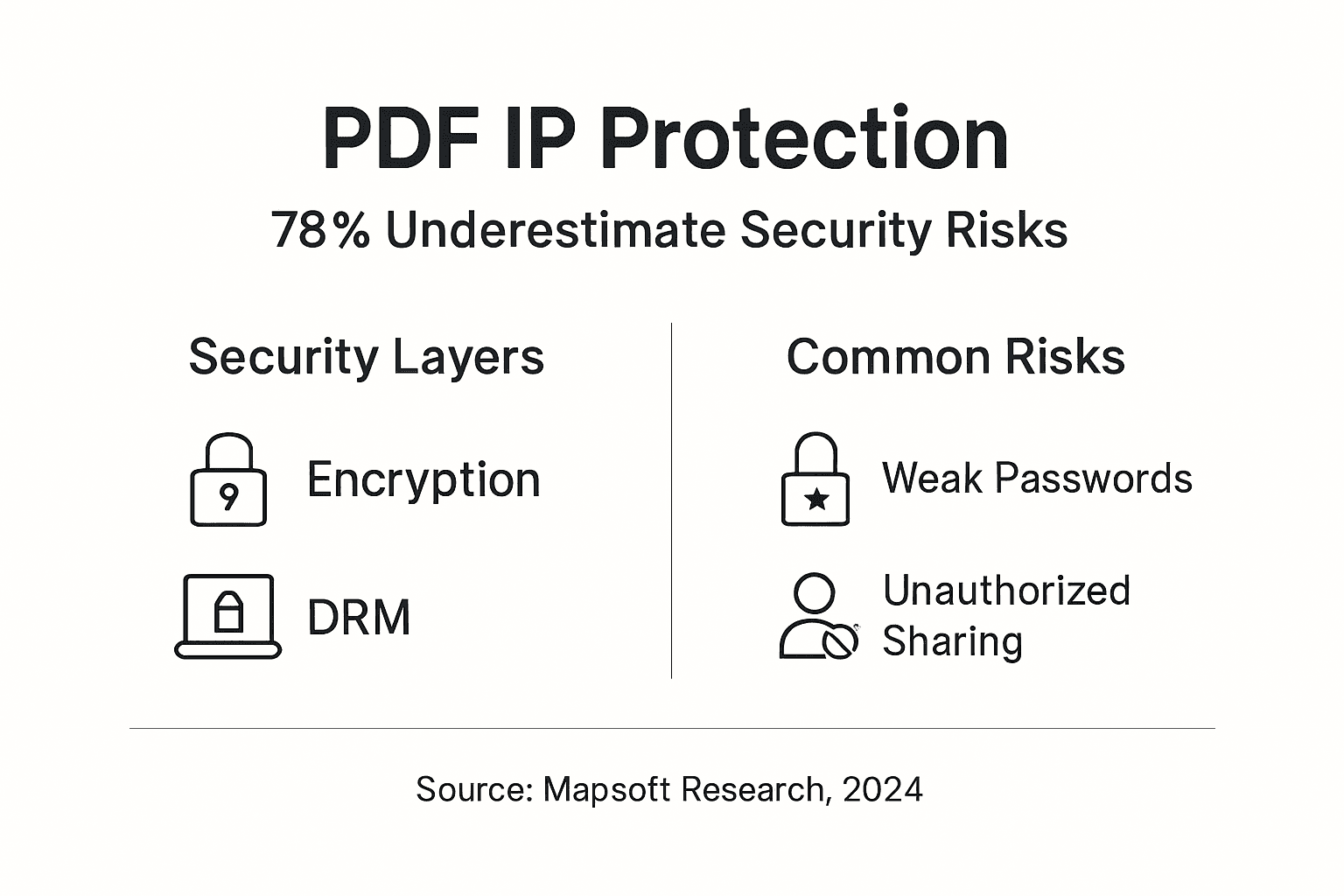
Enterprise PDFs contain trade secrets, proprietary designs, and strategic plans worth millions, yet 78% of enterprises underestimate the sophistication of attacks targeting this intellectual property. Simple password protection no longer suffices in an era of advanced cracking tools and persistent threat actors. This article explores technical encryption methods, DRM controls, automated workflows, and legal frameworks that IT managers need to implement comprehensive PDF IP protection strategies.
Table of Contents
- Introduction To PDF Intellectual Property Protection
- Technical Mechanisms To Protect PDFs
- Role And Implementation Of Digital Rights Management For PDFs
- Automated Workflows For PDF Security In Enterprise Environments
- Legal And Regulatory Frameworks Governing PDF Intellectual Property
- Common Pitfalls And Misconceptions In PDF IP Protection
- Practical Implementation Strategies For Protecting PDF Intellectual Property
- Conclusion: Bridging Security And Usability In PDF IP Protection
- Explore Advanced PDF Security And Workflow Solutions
- Frequently Asked Questions
Key Takeaways
| Point | Details |
|---|---|
| Strong encryption is foundational | AES 256-bit encryption provides military-grade protection against unauthorized access and content extraction |
| DRM enables granular control | Digital rights management systems enforce time limits, printing restrictions, and dynamic usage policies beyond passwords |
| Automation scales security | Workflow automation reduces manual errors by over 30% while ensuring consistent application of security measures |
| Legal frameworks vary globally | Protection strategies must account for varying domestic laws and international treaty enforcement challenges |
Introduction to PDF Intellectual Property Protection
PDFs have become the universal container for sensitive intellectual property, from engineering specifications to financial projections. The format’s ubiquity creates substantial risk exposure. Unauthorized access enables competitors to extract trade secrets, while uncontrolled distribution allows proprietary content to spread beyond intended recipients.
Digital transformation has accelerated document sharing across cloud platforms, partner networks, and remote workforces. This increased velocity of PDF circulation amplifies IP exposure exponentially. Traditional perimeter security no longer protects documents once they leave controlled environments.
The stakes are substantial. Leaked product roadmaps can destroy competitive advantages. Stolen research data represents years of investment lost. Enterprises face several critical risks:
- Unauthorized copying and redistribution of proprietary content
- Content extraction through basic copy-paste or advanced parsing tools
- Printing and photographing of supposedly protected documents
- Credential sharing that bypasses intended access controls
- Metadata exposure revealing sensitive organizational information
Protection strategies must evolve beyond basic passwords to address sophisticated attack vectors. Layering multiple security mechanisms creates defense in depth that withstands determined adversaries while maintaining usability for legitimate users.
Technical Mechanisms to Protect PDFs
Encryption forms the foundation of PDF security by rendering content unreadable without proper credentials. Yet not all encryption approaches deliver equivalent protection. Understanding technical differences guides appropriate selection.
Password protection represents the most basic approach, splitting into user passwords for opening documents and owner passwords for restricting actions. However, password-only security remains vulnerable to brute force attacks and social engineering. AES 256-bit encryption provides significantly stronger protection through military-grade cryptographic algorithms that resist computational cracking attempts.
Certificate-based security elevates protection by tying access to digital identities rather than shared secrets. Public key infrastructure validates user identity before decrypting content. This approach prevents password sharing and provides audit trails linking document access to specific individuals.
| Security Method | Strength Level | Identity Verification | Resistance to Sharing |
|---|---|---|---|
| Password Protection | Low to Medium | None | Low |
| AES 256-bit Encryption | High | Optional | Medium |
| Certificate Security | Very High | Required | High |
Implementation matters as much as selection. Weak passwords undermine even AES encryption, while certificate systems require proper PKI infrastructure. Key management becomes critical as enterprises scale, requiring secure storage and rotation policies.
Pro Tip: Combine AES encryption with certificate-based access controls for documents containing high-value IP. The dual authentication layer stops both casual breaches and determined attacks while creating forensic trails for incident response.
The technical foundation must integrate seamlessly with business workflows. Overly restrictive security creates workarounds that bypass protections entirely. Balance remains essential.
Role and Implementation of Digital Rights Management for PDFs
DRM systems extend beyond encryption by enforcing granular usage policies that persist with documents throughout their lifecycle. Where encryption controls whether you can open a file, DRM dictates what you can do after opening it.
Modern DRM capabilities include:
- View-only modes preventing copying, printing, or editing
- Print restrictions limiting copies or disabling printing entirely
- Time-limited access that automatically revokes document availability
- Dynamic watermarking identifying authorized users on each page
- Screen capture prevention blocking screenshot tools
DRM systems enforce detailed, dynamic usage policies and surpass password-only security by maintaining control after initial authentication. Policies follow documents even when forwarded or stored on unmanaged devices.
Consider a pharmaceutical company distributing clinical trial data. Basic encryption protects transmission, but DRM ensures reviewers can view findings without printing copies that might be photographed or mislaid. Time limits automatically revoke access when review periods end, eliminating lingering exposure from outdated documents.
Adobe Acrobat DRM integrations enable policy enforcement through familiar interfaces without requiring specialized viewers. This compatibility ensures adoption while maintaining security rigor.
Pro Tip: Implement tiered DRM policies matching document sensitivity levels. Public materials need minimal restrictions, while trade secrets require view-only modes with dynamic watermarking. Policy templates standardize appropriate protections across document classifications.
The distinction matters because DRM addresses threats encryption alone cannot stop. An encrypted PDF opened on an authorized device remains vulnerable to screen capture or unauthorized forwarding. DRM policies travel with content, maintaining protection regardless of storage location or access method.
Automated Workflows for PDF Security in Enterprise Environments
Manual security application creates inconsistency and human error. Workflow automation reduces manual errors by over 30% while ensuring uniform protection across thousands of documents.

Automated PDF security workflows handle repetitive tasks at scale. Batch processing applies encryption, watermarks, and redactions across document repositories simultaneously. This consistency eliminates the risk that sensitive files slip through gaps in manual procedures.
Audit trails represent another critical automation benefit. Logging every document access, modification, and sharing action creates forensic records for compliance and incident investigation. Automated systems track who opened which documents when, building comprehensive access histories without manual record keeping.
API integration with Adobe environments enables automation in PDF workflows through programmatic control. Scripts trigger security application based on document metadata, content classification, or distribution channels.
A robust automated workflow follows these steps:
- Document creation triggers classification based on content analysis or creator designation
- Automated system applies encryption and DRM policies matching classification level
- Dynamic watermarking embeds user identity and access timestamp
- Audit logging records security application and initial authorized users
- Distribution system enforces access controls and tracks sharing
- Periodic review flags documents requiring policy updates or access revocation
Pro Tip: Start automation with high-volume, low-complexity scenarios like standard contracts or recurring reports. Success builds confidence before tackling nuanced edge cases requiring human judgment.
The efficiency gains prove substantial. Security teams protecting tens of thousands of PDFs cannot manually review each document. Automation ensures comprehensive coverage while freeing experts to address exceptions and policy refinement.
Legal and Regulatory Frameworks Governing PDF Intellectual Property
Technical protections operate within legal contexts that determine enforceability and remedies. Understanding applicable laws shapes both protection strategies and incident response plans.
In the United States, the Defend Trade Secrets Act (DTSA) protects digital trade secrets including PDFs containing proprietary information. This federal protection enables civil litigation against misappropriation, provided owners demonstrate reasonable efforts to maintain secrecy. Technical controls like encryption and access restrictions evidence such reasonable efforts.
Copyright law provides automatic protection for original works fixed in PDFs, though registration strengthens enforcement. Patent protections may apply to inventions disclosed in technical documents. Each framework imposes different requirements and offers distinct remedies.
AI-generated PDF content presents new IP ownership challenges requiring updated legal protections. Current laws evolved around human authorship, creating ambiguity when algorithms generate substantial portions of document content. This uncertainty affects both ownership claims and infringement defenses.
International operations complicate matters significantly. Cross-border enforcement of PDF IP rights faces jurisdictional challenges and treaty gaps. A document protected under U.S. law may receive different treatment in jurisdictions with weaker IP frameworks or varying fair use doctrines.
| Legal Framework | Geographic Scope | Primary Protection | Key Limitations |
|---|---|---|---|
| Defend Trade Secrets Act | United States | Trade secrets in commerce | Requires reasonable secrecy efforts |
| Copyright Law | Berne Convention signatories | Original expression | Does not protect ideas or facts |
| Patent Protection | Country-specific | Novel inventions | Requires formal application and disclosure |
| International Treaties | Varies by agreement | Cross-border coordination | Enforcement depends on local courts |
PDF legal compliance frameworks require coordinating technical controls with legal requirements. Encryption demonstrates reasonable secrecy efforts. Audit trails provide evidence for litigation. Access restrictions show intent to maintain confidentiality.
The intersection of technology and law demands attention. Technical protections without legal foundations leave gaps. Legal claims without technical evidence face challenges proving damages or demonstrating protection efforts.
Common Pitfalls and Misconceptions in PDF IP Protection
Widespread misunderstandings undermine PDF security despite good intentions. Recognizing these myths prevents false confidence in inadequate protections.
Myth: Password protection alone secures PDFs adequately. Reality differs substantially. Basic password protection remains vulnerable to common cracking techniques and provides no protection against authorized users redistributing content. Passwords get shared, reused, and compromised. Treating password protection as complete security creates dangerous exposure.
Effective alternative: Layer AES encryption with certificate-based access and DRM controls. Multiple authentication factors and usage restrictions compensate for individual weaknesses.
Myth: DRM and password protection are equivalent approaches. This confusion stems from both requiring authentication. However, DRM enforces ongoing usage policies while passwords simply gate initial access. Once you open a password-protected PDF, no technical controls prevent copying content or taking screenshots. DRM maintains restrictions throughout the document lifecycle.
Effective alternative: Implement DRM for sensitive documents requiring usage control beyond viewing. Reserve simple passwords for low-value content where convenience outweighs risk.
Myth: Legal frameworks provide uniform, straightforward IP protection. International operations reveal this fallacy quickly. Laws vary dramatically across jurisdictions. What constitutes trade secret protection in one country may receive no recognition elsewhere. Treaty enforcement proves slow and uncertain.
“Understanding that legal protections vary by jurisdiction is critical for global enterprises. Technical controls provide consistent security regardless of legal environment, making them essential complements to legal strategies.”
Effective alternative: Build technical protections that function independently of legal frameworks. Use legal remedies as backstops rather than primary defenses. Maintain documentation supporting claims across multiple jurisdictions.
These misconceptions share a common thread of oversimplification. Effective PDF IP protection requires nuanced, layered approaches acknowledging that no single mechanism provides complete security.
Practical Implementation Strategies for Protecting PDF Intellectual Property
Translating principles into practice requires systematic approaches balancing security rigor with operational reality. Successful implementations layer multiple protections while maintaining usability.
The core strategy combines encryption, DRM, watermarking, and workflow automation into integrated defense in depth. Each layer addresses different threat vectors:
- Encryption stops unauthorized access and protects transmission
- DRM controls usage by authorized recipients
- Watermarking enables leak tracing and deters redistribution
- Workflow automation ensures consistent application
Implementation proceeds systematically:
- Classify documents by sensitivity and required protection levels
- Define standard policies matching each classification tier
- Configure automated workflows applying appropriate protections
- Implement audit logging capturing all document interactions
- Train users on security requirements and proper handling
- Monitor compliance and investigate anomalies
- Review and update policies as threats evolve
Different scenarios demand tailored approaches. Highly sensitive R&D documents require maximum restrictions, while archived materials need preservation over active protection.
| Document Type | Encryption | DRM Controls | Watermarking | Expiration |
|---|---|---|---|---|
| Active R&D | AES 256 + certificates | View only, no print | Dynamic per user | 90 days |
| Archived records | AES 256 | Print allowed | Static document ID | None |
| Published materials | Optional | Minimal | Branding only | None |
Watermarking and redaction help trace leaks and prevent unauthorized redistribution of PDF IP. Dynamic watermarks embedding user identity and access timestamps create accountability. Knowing that leaked documents trace back to specific individuals deters intentional disclosure.
Pro Tip: Leverage Adobe Acrobat integration and custom plugins to enforce security policies within existing workflows. Users adopt protections more readily when tools feel familiar rather than requiring new platforms.
The goal remains protecting IP without crippling productivity. Overly restrictive controls drive workarounds that bypass security entirely. PDF workflow automation balances protection and usability by embedding security into natural document lifecycles.
Scaling these strategies across enterprises requires central policy management, automated enforcement, and continuous monitoring. Manual approaches fail when dealing with thousands of documents and hundreds of users.
Conclusion: Bridging Security and Usability in PDF IP Protection
Effective PDF intellectual property protection demands multi-layered strategies combining robust encryption, granular DRM controls, automated workflows, and legal compliance. No single mechanism suffices against determined adversaries or addresses all threat vectors.
The challenge lies in maintaining security without sacrificing usability. Overly restrictive controls create frustration and workarounds that undermine protection efforts. Successful implementations balance rigor with operational reality through intelligent automation and policy tiering.
Emerging technologies and evolving legal frameworks require ongoing vigilance. AI-generated content, cloud collaboration, and cross-border enforcement present challenges that yesterday’s approaches cannot address. Enterprises must continuously adapt protection strategies while monitoring threat landscapes and regulatory developments. The investment in comprehensive PDF IP protection pays dividends through preserved competitive advantages and avoided losses from preventable breaches.
Explore Advanced PDF Security and Workflow Solutions
Protecting your PDF intellectual property requires more than theory. It demands proven tools that scale with enterprise needs while maintaining security rigor.
Mapsoft delivers comprehensive solutions automating enterprise PDF workflows with integrated encryption, DRM controls, and batch processing capabilities. Our PDF workflow automation tools reduce manual errors while ensuring consistent security application across your document repositories. Leverage Adobe Acrobat advanced techniques through specialized plugins and APIs that extend platform capabilities without disrupting existing workflows. Our solutions bridge security requirements with operational efficiency, enabling you to protect intellectual property while maintaining productivity.
Frequently Asked Questions
What is the difference between PDF encryption and DRM?
Encryption protects the PDF file itself, making content unreadable without the correct key or password. DRM controls what users can do after opening an encrypted file, enforcing restrictions on printing, copying, editing, and sharing. Encryption secures transmission and storage, while DRM governs usage and maintains control throughout the document lifecycle.
Can workflow automation tools integrate with existing Adobe Acrobat environments?
Yes, modern workflow automation platforms integrate seamlessly with Adobe Acrobat through APIs, plugins, and SDKs. These integrations enable automated security application, batch processing, and policy enforcement within familiar Acrobat interfaces. Users continue working with standard tools while automation handles security consistency in the background.
How do international laws affect PDF IP protection strategies?
International laws vary significantly in IP definitions, enforcement mechanisms, and treaty obligations. A document protected as a trade secret in the US may receive different treatment in jurisdictions with weaker frameworks. Effective strategies layer technical protections that function regardless of legal environment, using laws as supplementary rather than primary defenses.
What are best practices for watermarking PDFs to deter leaks?
Dynamic watermarks embedding user identity, access timestamps, and document IDs create accountability and enable leak tracing. Position watermarks prominently enough to deter screenshots without obscuring content. Combine visible watermarks with invisible forensic marks for additional tracing capabilities. Update watermarks on each access to maintain current user associations.
Are AI-generated PDF contents protected under current IP laws?
Current laws provide ambiguous protection for AI-generated content because they evolved around human authorship concepts. Copyright protection may be limited or unavailable depending on the AI’s role in creation. This uncertainty creates risks for both ownership claims and infringement defenses. Enterprises should document human creative contributions and maintain evidence of substantial human involvement in AI-assisted document creation.



